In today’s digital world, data goes beyond just being files and numbers. It embodies the trust your customers have in you and serves as the backbone of your business. At QAIRO, we believe that security shouldn’t be an afterthought; it’s woven into every system we create from the very start. Our approach is deliberate, considerate, and crafted to safeguard you not just for today, but for the long haul.
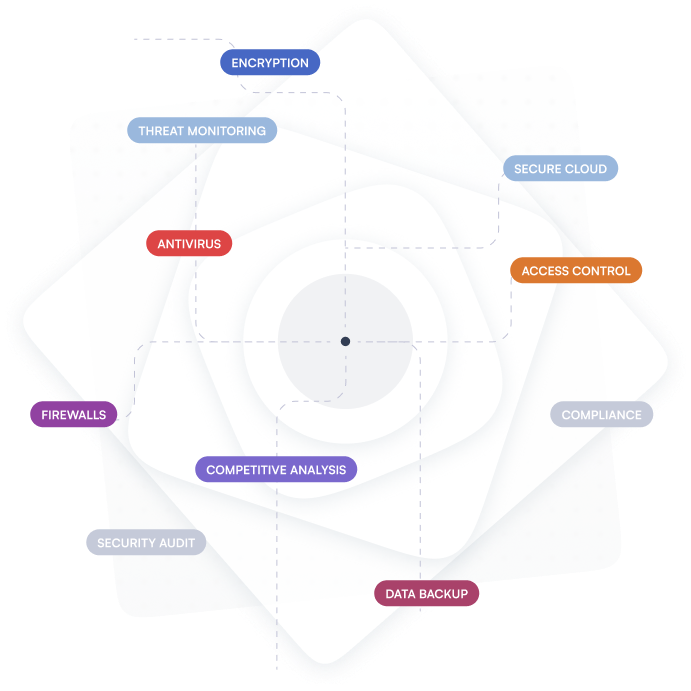
We concentrate on three key principles: preventing risks before they escalate into issues, providing you with complete visibility into your systems, and making sure you’re ready for any challenges that may arise.
What’s the outcome? Your data remains secure, access is tightly controlled, and your systems are robust as new threats emerge. Our security solutions operate seamlessly in the background, ensuring they do their job without interrupting yours. This allows your teams to concentrate on growth, innovation, and daily tasks, all while feeling assured that everything behind the scenes is secure, compliant, and stable.

Your data remains protected at every stage, across all communication channels.
Access is granted strictly based on responsibility—nothing more, nothing less.
Constant monitoring ensures quick detection and response to potential risks.
Hardened cloud environments with routine audits and security assessments.
Designed to meet industry standards and regulatory expectations.
Regular backups and recovery plans to keep your operations running without interruption.